How does the NIS2 directive relate to IDM systems, and how do IDM systems support regulatory compliance?
![]() Mónika Bikki
Mónika Bikki
![]() 2024.10.17
2024.10.17

The European NIS2 directive (Directive (EU) 2022/2555) strengthens cyber defense capabilities across the Union by imposing strict cybersecurity requirements on both large companies and SMEs. This includes managing security risks, reporting incidents, and maintaining auditability. Identity Management (IDM) systems play a crucial role in meeting these requirements by providing comprehensive authorization management and regulatory compliance.
Key Requirements of NIS2 and IDM Solutions
Risk Management and Secure Access: NIS2 mandates technical and organizational measures to manage cyber risks. IDM systems fulfill this by providing strict access control and automated audits.
Incident Reporting: The directive requires reporting cyber incidents within 72 hours. IDM systems help detect unauthorized access attempts and ensure timely reporting.
Auditability: IDM systems log all access changes and user activities, supporting the audit and documentation needs of NIS2.
IDM’s Key Features for NIS2 Compliance
Access Management: IDM systems ensure that only authorized individuals can access data, using role-based access control (RBAC), the Least Privilege Principle, and automated lifecycle management.
Audit and Reporting: These systems facilitate regulatory compliance by generating detailed reports on user activities, making it easy to demonstrate adherence to NIS2.
Incident Response: IDM systems detect and manage unauthorized activities, supporting fast responses to minimize risks.
The IdMatrix SBE System
The IdMatrix SBE system we offer places a strong emphasis on flexibility and ease of use right from the design phase. It has a built-in HR module that is ready to use immediately after installation, independent of any HR system integration. AD, Exchange automatically manages privileges and allows manual privilege management for systems that do not have an interface.
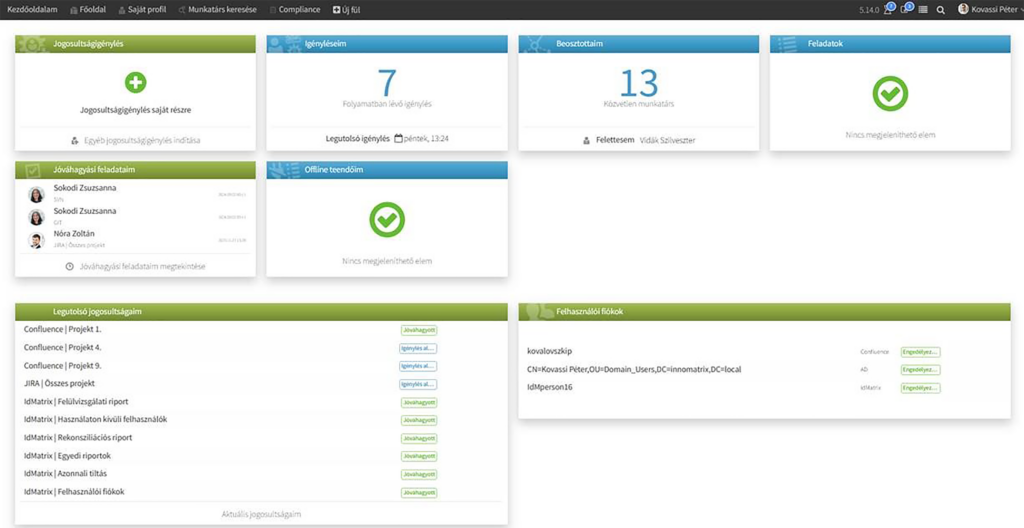
Additionally, IdMatrix SBE provides scalability to accommodate both small and large organizations, seamless integration with other security tools for comprehensive monitoring, and central management of user authorizations to simplify processes and minimize errors.
Implementing IDM systems enhances overall cybersecurity by automating security processes, reducing manual errors, and ensuring regulatory compliance through scalable and integrative solutions.

