From alert to decision in minutes
![]() Ádám Karóczi
Ádám Karóczi
![]() 2026.02.20
2026.02.20

SOCs are under pressure: alert volumes keep rising, infrastructures are more complex, and attackers adapt faster—often with AI support. In many teams, the biggest bottleneck isn’t tooling, it’s analyst time. The most expensive minutes are spent on incident “data mining”: collecting context, connecting events, building a timeline, and only then deciding whether an alert is real or a false positive.
This is where NetWitness AI Analyst (an agentic AI approach) helps: it takes over repetitive investigation preparation and delivers structured decision support—while keeping humans in control.
Why earlier automation approaches often fall short
SOAR promised automation through playbooks, but many teams hit similar limits:
- playbooks take time to build and maintain,
- real investigations are hard to model in fixed steps,
- environments and attacker behavior change faster than workflows can be updated.
Prompt-based “AI assistants” can help, but they still require a human to drive a back-and-forth Q&A loop. That slows investigations and makes outcomes depend on individual prompting skills.
The agentic step: AI that completes investigation tasks
An agentic AI doesn’t just answer questions—it executes a full analytical task flow and produces an outcome the analyst can validate.
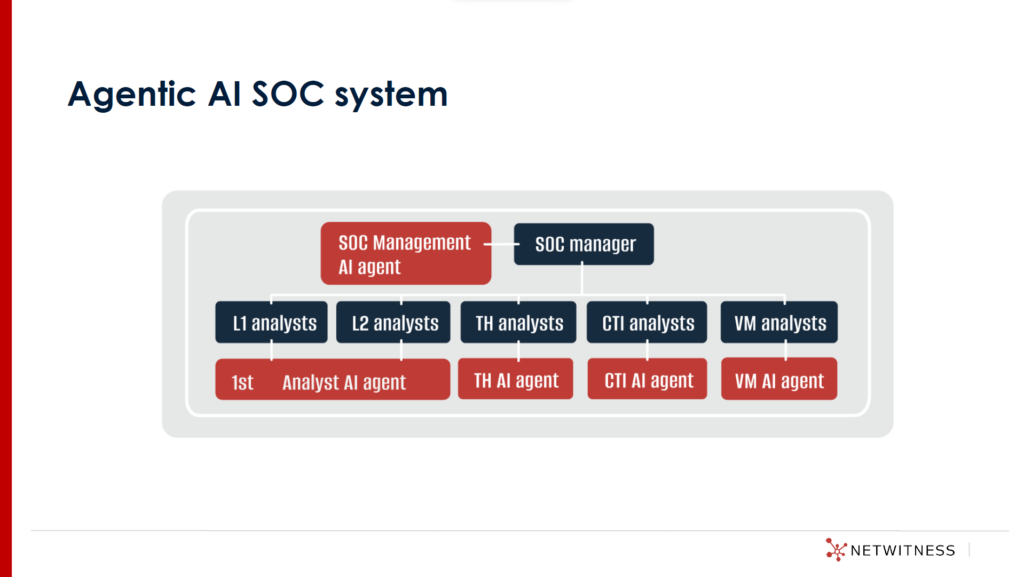
NetWitness’ broader concept is an AI ecosystem aligned with SOC roles (analyst, threat hunter, CTI, vulnerability, SOC manager). The goal is not replacement, but removing low-value work so experts can focus on decisions and improvement.
What AI Analyst does in practice
Investigations often start with a narrow SIEM signal (e.g., a connection to a “malicious” IP) that lacks context. Analysts then expand searches, pull logs from multiple places, correlate activity, and build the sequence of events—sometimes spending hours even if the result is a false positive.
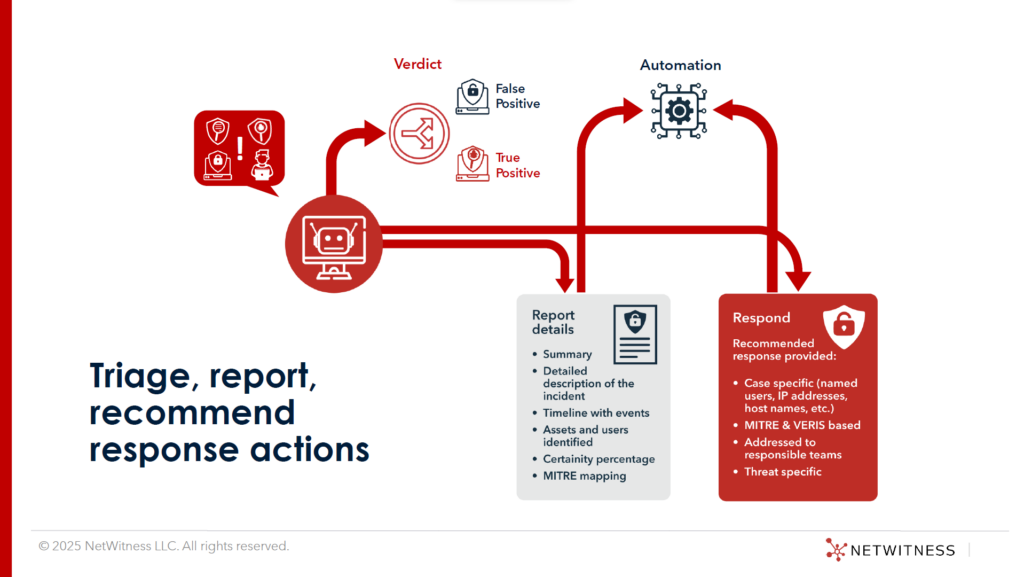
AI Analyst accelerates this by assembling a decision-ready investigation package:
- Context expansion: broadens the search in time and scope beyond the initial alert.
- Multi-source correlation: combines log, endpoint, and network events.
- Enrichment: adds internal context (asset criticality, identities/permissions) and external threat intelligence.
- Framework alignment: structures findings using established approaches such as MITRE ATT&CK, NIST, and VERIS.
- Playbook-light investigation: investigates many scenarios by default, with optional customer-specific tuning.
- Structured output: summary, timeline/attack chain, interpretation, recommended verdict (false vs. true positive), confidence level with justification, and suggested response steps.
- Integration support: results can be consumed via an API for downstream tools and workflows.
What changes operationally
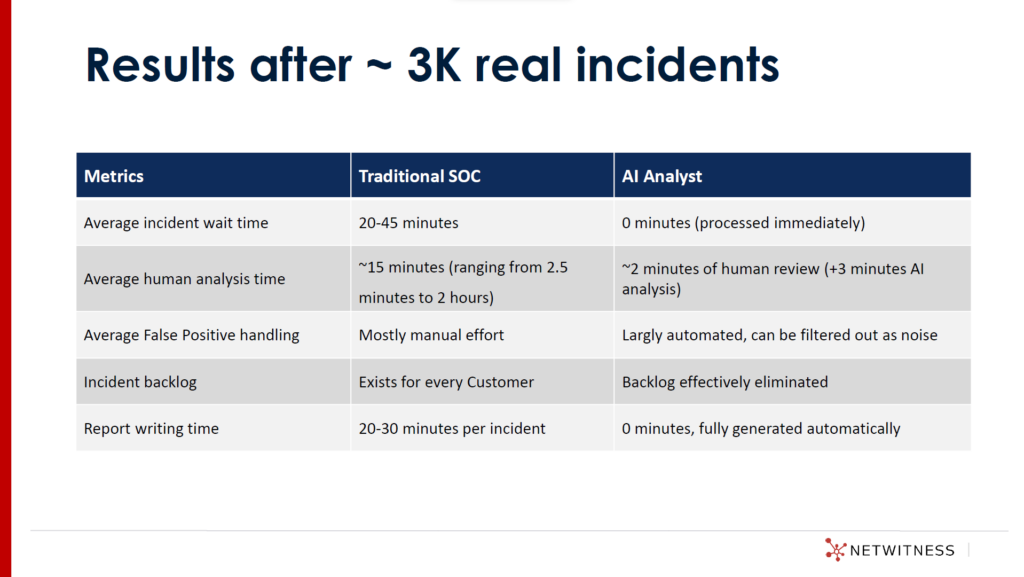
In a traditional SOC, an incident may wait 20–45 minutes before analysis begins. With AI Analyst, investigation can start immediately, reducing that waiting time. The goal is an initial analysis in ~3 minutes, followed by a few minutes for human validation and any extra searches.
Speed isn’t the only benefit. By using consistent structure and evidence-backed outputs, investigations become easier to review, hand over, and audit—reducing dependency on individual experience and helping prevent subtle patterns from slipping through triage.
Key takeaway from this approach
What’s important to understand is that agentic AI is not just a chat interface on top of security data. It is designed to execute the investigation workflow: collect evidence, correlate related events, enrich with internal context and external intel, and turn the result into a clear storyline (what happened, when, where, and why it matters).
Instead of leaving analysts with raw hits, it produces a reviewable package: the key entities involved, the suspected chain of activity, the affected assets/identities, and the log/telemetry references that support the conclusion.
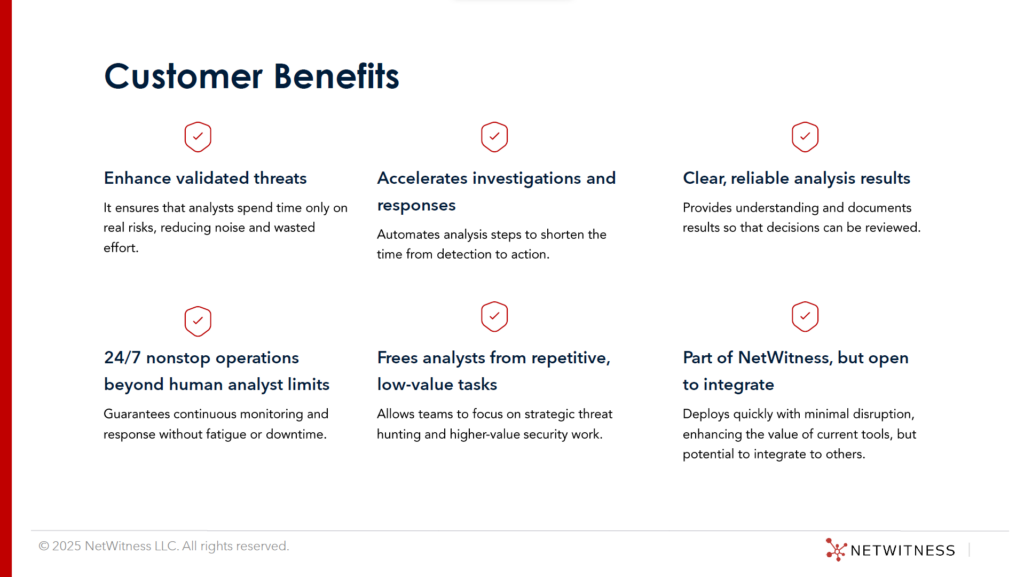
This changes daily operations. Analysts spend less time assembling context and more time deciding and responding—while final judgment stays with the SOC. The AI accelerates triage and preparation; the human validates the verdict and triggers the response.
The common lesson from the examples
In both scenarios, the turning point was the same: a single alert wasn’t enough. The outcome depended on rapid context-building across multiple data sources (users, hosts, network, identity, asset criticality, threat intel) to confirm what happened, what was affected, and what to do next.
What SOC teams gain
- Faster decisions, less backlog: less time gathering context, more time responding.
- Less burnout, more high-value work: more capacity for threat hunting, detection tuning, and process improvements.
- More consistent investigation quality: standardized reporting improves repeatability and governance.
Bottom line: The SOC time sink is moving from a raw signal to a verified story. Agentic AI compresses that stage and delivers a structured, verifiable investigation package—so analysts can reach confident decisions in minutes, not hours.
Read the full article on our International subsidiary’s website by clicking on the logo:


